
New, Rare and Unreleased Material from the DMZ Empire
New, Rare and Unreleased Material from the DMZ Empire



Rockets Away: the cycle of military confrontation continues

Kamala Harris at the DMZ and the Ghost of John Foster Dulles
JFK, Bob Dylan, and the Death of the American Dream

Key U.S. documents on Gwangju and the Rise of Chun
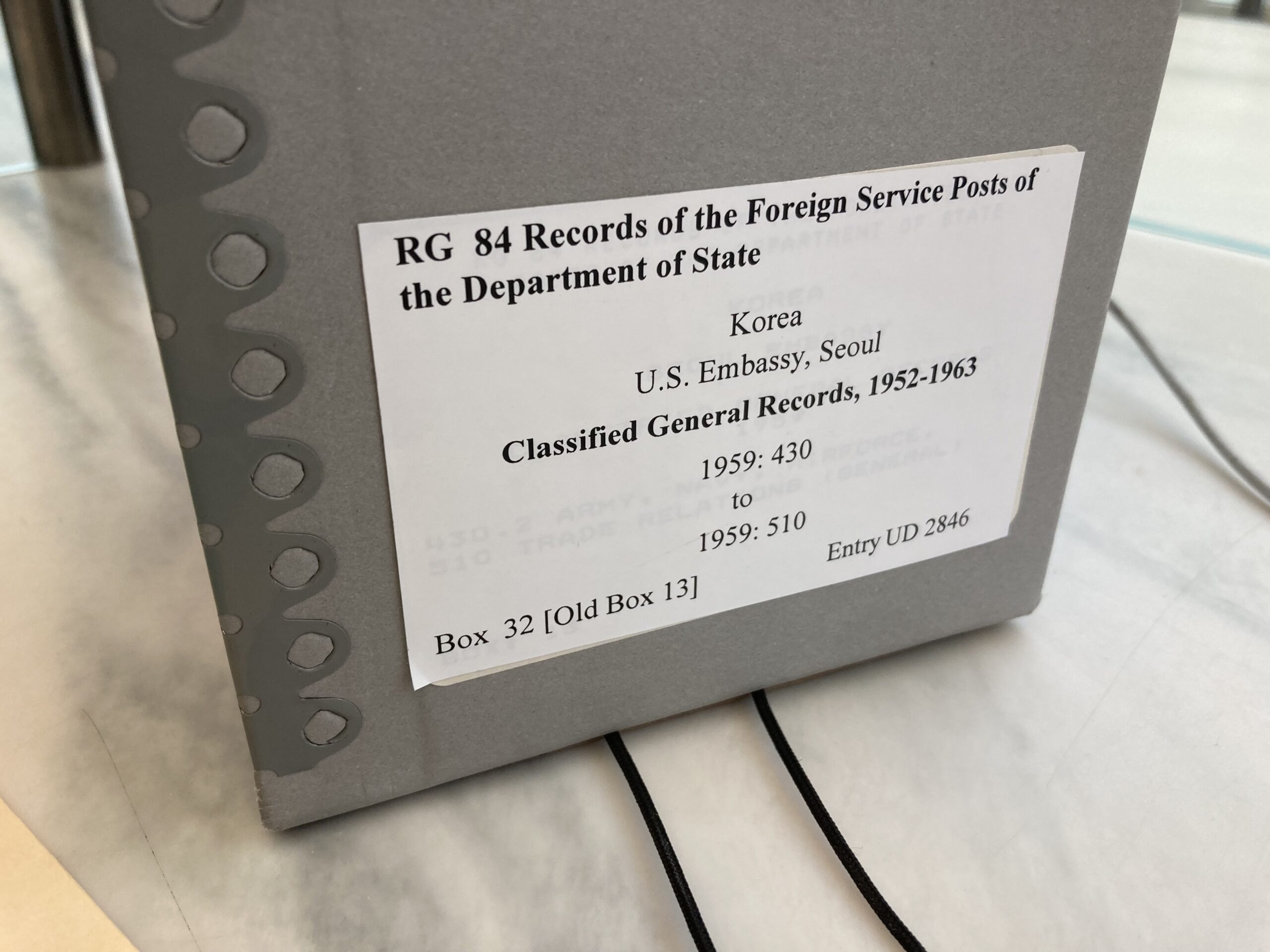
1947: “Comparative Costs – US and ROKA Soldier”
A 1947 comparison by the U.S. Embassy in Seoul of…
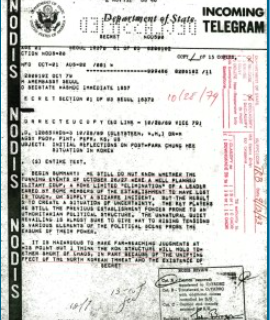
Cherokee Files: Key Document on Park’s Assassination
The assassination of Park Chung Hee on the night of…

Gleysteen’s talks with Chun Doo Hwan
BOX 2, FILE 7 (1979-1980) Ambassador Gleysteen’s discussions with Chun…
Ambassador Gleysteen: Key Policy Documents
BOX 2, FILE 6 (1979-1980) This file contains key documents…

White House: “The first priority is the restoration of order in Kwangju.”
BOX 2, FILE 4 (May 22, 1980) This document from…

ROK Diplomats Refuse to Send Congressional Letter to Blue House
BOX 2, FILE 3 (1980) July 1980 – These documents…
Smoking Guns: U.S. Intervention Exposed
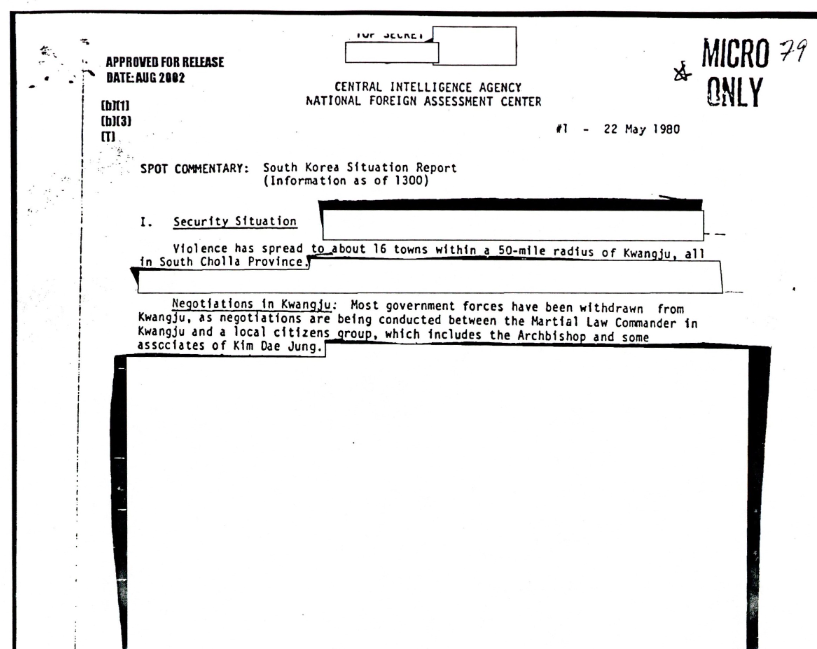
CIA Reports from Gwangju May 21-22, 1980
May 21 and May 22, 1980, were two of the…
Gwangju Archives | Cherokee Files | 1979-1980

Gwangju Archives | Aftermath | Arrests | Chun Visit
Gwangju Archives | Pentagon/DIA Reports
This is an online database of the 4,000 declassified US…
Gwangju Archives | First US Reports
This is the first posting of what will be an…

Debacle in Kwangju | The Nation | December 9, 1996
This article from The Nation about Gwangju from 1996 focuses…

Gwangju Presente!
May 18 marks the 40th anniversary of the Gwangju Massacre…
SOUTH KOREA, LIKE JAPAN, GETS JITTERY ABOUT IRAN
Abe’s Japan and its people are thinking twice about sending…